The Raritan Blog
Home » Raritan Blog
When Deploying a Centralized IT Management Solution, Leverage the Advantages of a Virtual Appliance
October 25, 2010
Vendors in the IT and data center space are beginning to make their centralized management systems available as a virtual appliance, enabling them to run on leading virtualization platforms. This is the case with Raritan’s CommandCenter Secure Gateway (CC-SG). A new version will be released in November that can be deployed as a VMware virtual machine.
Running as a virtual machine (VM) – especially within a VMware environment that delivers several key features rich in flexibility and security, has several operational advantages over a proprietary hardware solution. For example, there is likely space and resources available in an established virtual environment on which the appliance can be installed. As a result, additional hardware expense is avoided. Also, with a virtual appliance, there is no extended hardware warranty to purchase.
Raritan IT publishes measured power savings by Power IQ
Allen Yang
October 22, 2010
In late August 2010, I wrote on this blog last time that Raritan IT will use Power IQ and PX to monitor the incremental power consumption of the Cisco UCS, while we gradually migrate some physical rack-mount physical servers as VM onto UCS blades. The following results reflect our P2V migration activities between 2010-08-05 and 2010-10-20. We have 2 UCS chassis that we call UCS1 and UCS2, and both of them are installed on our Cisco Rack 4. During the time period from 08/05 to 10/20, we had the following physical activities:
- 08/11: Turn on two blades on UCS for Engineering testing
- 08/15: Turn on 2nd 10Gib port on Fabric Interconnect
- 08/30: Remove 2 VMware ESX Servers (the 2 Dell PowerEdge 1950)
- 09/01: Turn 1 additional blade on UCS2 to measure its effect on power consumption
- 09/03: Remove SharePoint Test Server (a Dell PowerEdge 2850) and DNS2 (a 1U PC-server)
- 09/14: Migrate BES as a VM onto UCS blade (an HP Proliant DL140)
- 09/20: Migrate Exchange Server (a Dell PE1950) as a VM onto UCS blade; turn testing blade off
- 10/11: Turn one UCS blade on for Oracle JDE remote DR site
From Power IQ data reading we have the following observations:
- Each UCS blade we have consumes roughly 4.3 KWh per day. This is somewhat consistently demonstrated from measuring the total power consumption of the observed systems including the 2 UCS chassis and the non-UCS physical servers. On 08/11, the measurement was 334.6 KWh. On 08/12, 24-hours later after turning on 2 UCS blades, the measurement was 339.7KWh. Since then the UCS power consumption stayed at that level until the next even on 08/15. This 4.3KWh incremental power consumption per UCS blade per day was also consistently measured between 09/01 and 09/02 when IT turned on the 3rd blade on UCS2 to measure incremental power consumption.
- Migrating mildly loaded physical rack-mount servers as VMs onto the UCS blades typically doesn’t increase much power consumption. We Installed VMware ESX host on UCS and migrated two physical application servers onto UCS blade, and we couldn’t even find material difference before and after adding these 2 VMs onto UCS. But the power savings from decommissioning physical servers can be clearly seen. On 08/30, we removed 2 ESX host physical servers (Dell PowerEdge 1950), the total power consumption dropped by 6.55KWh a day. Then on 09/03, we removed another PowerEdge 2850 (a Sharepoint test Server) and a 1-U PC server (DNS); and we saw a drop of power consumption by 7.2KWh a day. Therefore, we see a clear power saving advantage from migrating physical servers into VMs.
- The new version of Power IQ is very helpful in data exporting and giving power consumption insights at various levels of details. We captured several diagrams from Power IQ to see the trend over time, then right from there we export the data into Excel spreadsheet, and we can examine the day by day details in there.
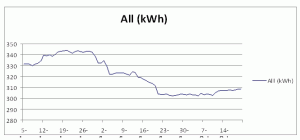
In summary, between 08/05 and 10/20, Raritan IT measured power saving of 20KWh a day with the activities of migrating 5 physical servers as VMs onto Cisco UCS blades and remove these physical servers from the racks. The daily power consumption of these observed systems combined dropped from slightly over 330KWh a day on 08/05 to slightly under 310 KWh a day on 10/20. The Power IQ trend diagram also portrays such gradual reduction, which very accurately reflects the activities conducted and the resulting effects on power consumption over the observed time period.
Power Consumption from Aug 5, 2010 to Oct 20, 2010
Raritan IT will continue its physical server migration activities in the next few months, there may be more interesting findings we can gather in the future; stay tuned.
(part of this blog entry is also posted in response to a comment for my late August blog post)
Raritan will be at the Green Data Center Conference in NYC on October 20th and 21st
Dorothy Ochs
October 11, 2010
Raritan will be at the Green Data Center Conference on Oct. 20-21, 2010 at the Embassy Suites New York (102 North End Avenue, New York, NY). Come check us out to learn about the latest in power management solutions.
Raritan is co-presenting "400V Data Center Solutions" with Starline at the Sept. 30th DatacenterDynamics show in Chicago.
Dorothy Ochs
September 15, 2010
We will be displaying our intelligent PDU’s, KVM-over-IP switch, and DCIM solutions in our booth. Stop by and visit us - you’ll be entered into our drawing for a Canon digital camcorder. For more information and to register: https://www.datacenterdynamics.com/en/conferences/.
What to Look for in a Smart Card-Enabled KVM Solution
September 13, 2010
With the release of the U.S. federal government’s HSPD-12 directive a few years ago, many CIO’s and IT managers found themselves with a key issue to address: how to authenticate both local and remote IT personnel as they access government servers and networks. HSPD-12 mandates secure, authenticated access to all federal information systems and buildings. While smart cards were already in use in several industries worldwide, their use really exploded when the U.S. Department of Defense responded to HSPD-12 by utilizing smart card technology as the basis for implementing its Common Access Card program (CAC). More recently, the DoD introduced a new type of smart card known as a Personal Identity Verification card (PIV), which must conform to the FIPS-201 standard.
Using a smart card to access a PC or server that’s within arm’s reach is easy. However, a major challenge is to support this directive in the data center or any application in which users must access multiple servers or PCs that are often located in a separate room, let alone several feet away. It’s inefficient to connect a smart card reader to each device and insert the card each time access is needed. In fact, it’s usually not possible to do so. In many cases, users need to access servers in inaccessible rooms – and with different security levels.
To meet this need, several smart card-enabled KVM solutions have been introduced by the industry’s primary vendors. Of course, no two are exactly alike, so what do you need to look for? It’s important to choose not only a solution that fulfills the basic requirement of supporting smart card authentication to multiple servers from a single location, but also one that makes the necessary feature adjustments that meet and exceed the highly secure operation requirements inherent of a smart card environment.
Subscribe
Upcoming Events
Latest Raritan News
- Legrand Wins Back-to-Back Awards for Intelligent Rack Power Distribution Innovation
- Posted on June 25, 2024
- Legrand Certifications and Process Controls Provide Confidence in Information Security for Network-Connected Devices in Data-Related Applications
- Posted on March 5, 2024
- Legrand Releases Version 4.0 of Raritan’s Industry-Leading Secure KVM Switches, Raising Bar for Secure Desktop Access
- Posted on July 31, 2023
- Legrand Revitalizes Data Center Sector with Two Revolutionary Intelligent Rack PDUs
- Posted on May 1, 2023
- Raritan Reveals The MasterConsole® Digital Dual KVM Switch
- Posted on February 18, 2021